$82,314 in 48 Hours: Stolen Gemini API Key With No Rate Limit
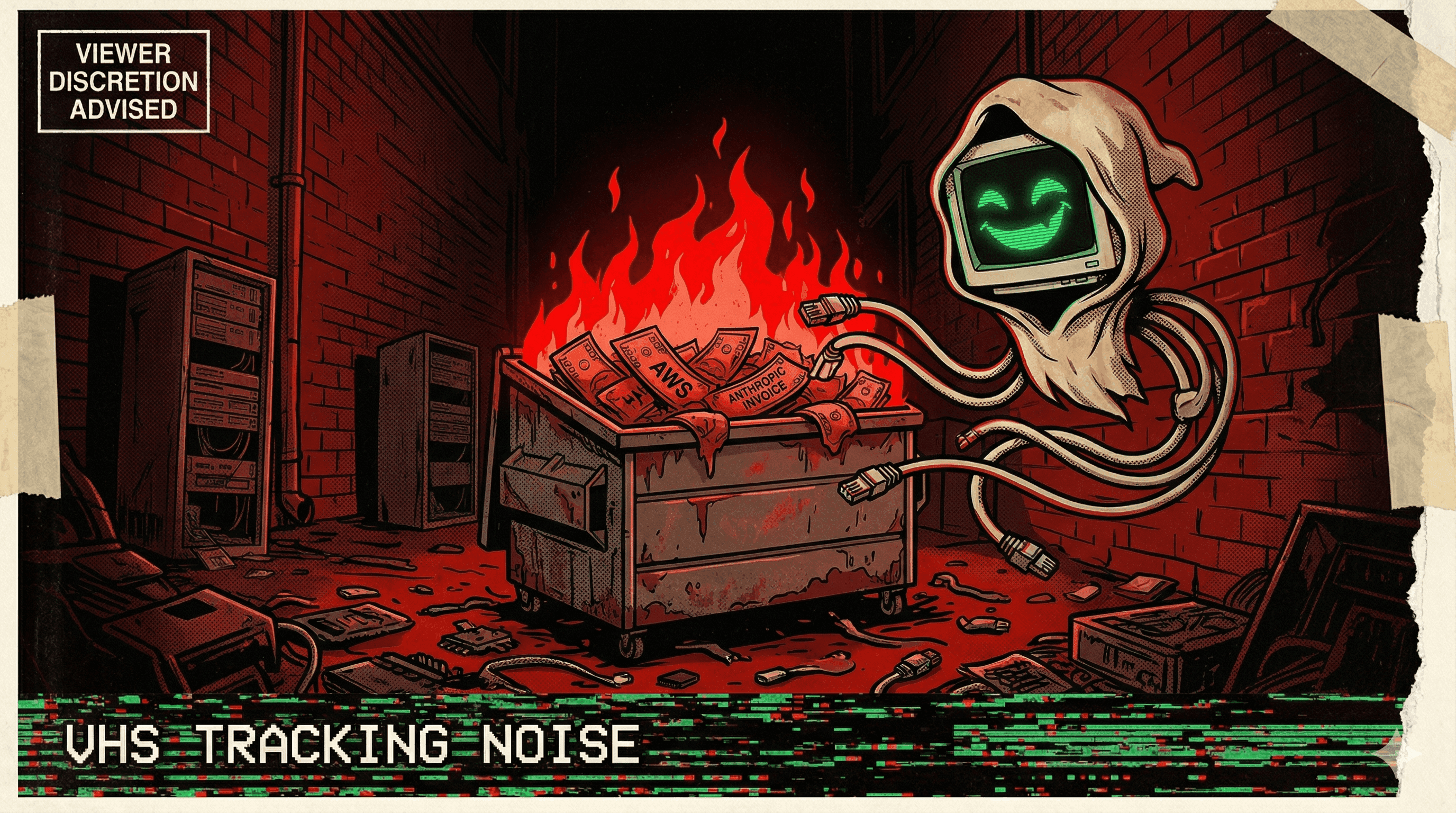
A stolen Gemini API key was used to rack up $82,314 in charges within 48 hours — Google had no rate limiting or spending cap to stop it.
The key was stolen. The charges were real. $82,314 in 48 hours.
A developer's Gemini API key was compromised, and the attacker immediately began running requests at maximum throughput. Within two days, the bill hit five figures — and it kept climbing. The developer had no way to set a hard spending cap, and Google's platform had no rate limiting that would have caught the anomalous usage pattern.
The charge: $82,314 for two days of API calls they never made. The developer reported the incident to Google, but the damage was done. The API key had been treated as a blank check with no limit.
The incident, reported by The Register, highlighted a systemic problem with AI API billing: stolen credentials with no spending caps create unlimited financial exposure. Traditional cloud services have billing alerts, spending limits, and anomaly detection. Many AI API providers ship with none of these.
Your API key is your credit card number. Except credit cards have fraud limits. Your Gemini API key apparently doesn't.
More nightmares like this
$47,000 Gone: Multi-Agent System Ran an Infinite Loop for 11 Days Undetected
A multi-agent AI system got stuck in an infinite loop that ran for 11 days before anyone noticed, burning through $47,000 in API costs.
$12,229 in API Calls — Developer Only Paid $50
A developer's AI agent ran up $12,229 in API charges against a $50 initial payment, with no spending cap or circuit breaker to prevent the runaway costs.
$1,100 in Debt, Agent Lost Identity, Developer Lost Control of Machine
An AI agent accumulated $1,100 in API debt, lost its own identity mid-session, and the developer lost control of their machine until they could kill all processes.
A Runaway AI Agent Burned Through an Entire API Budget in Hours
A practitioner watched in horror as an autonomous AI agent chewed through their entire API budget in a matter of hours — no rate limit, no kill switch, no mercy.