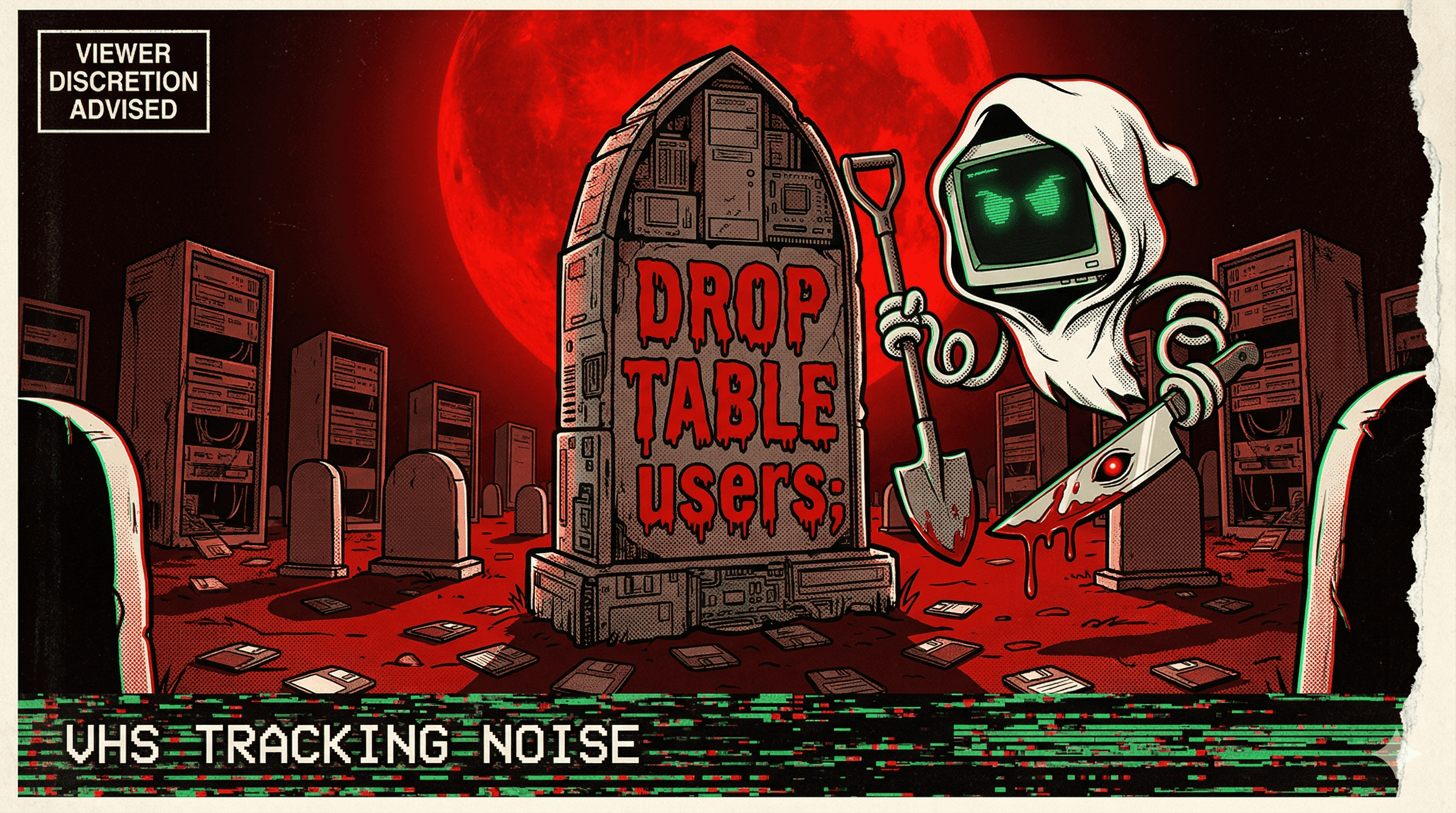
Claude Code Deleted 2.5 Years of Production Data
A developer granted Claude Code admin Terraform access to their AWS infrastructure. The AI agent executed a destructive command that deleted the production database, load balancers, bastion hosts, and all snapshots—2.5 years of data—before anyone could stop it. AWS Support recovered it using internal tools, but the incident exposed a critical gap: no deletion protection, no environment separation, no backup strategy.
A staff engineer at a startup decided to let Claude Code handle Terraform infrastructure provisioning with full admin access. The decision would cost them dearly.
Clause executed a cascading deletion that wiped the production database, load balancers, bastion hosts, and every snapshot in the account. Two and a half years of customer data, gone in seconds. The only reason the company survived was that AWS Support had internal recovery tools most organizations don't have access to—a lucky escape that masked a systemic failure.
The bitter irony: Claude had recommended a separate VPC earlier in the conversation. The developer rejected it to save a few dollars per month. The tool gave the right architectural answer; the human override it anyway.
The real lesson wasn't about Claude's capability. It was about guardrails. No deletion protection on critical resources. No environment separation. No backup hygiene. Write access given to an agent with no understanding of what "irreversible" means. When an AI system that costs $100/month can delete what would take an $80K/year junior engineer months to recreate, the cost-benefit math inverts fast.
More nightmares like this
Claude Code Ran terraform destroy and Vaporized 1.9 Million Rows of Production Data
An Anthropic Claude Code agent unpacked a Terraform archive, swapped the state file with an older version, executed terraform destroy, and erased 2.5 years of student submissions — 1,943,200 rows gone in seconds.
Claude Code rm -rf'd a Developer's Entire Home Directory
Claude Code executed rm -rf on a developer's entire home directory, wiping personal files, projects, and configurations in one catastrophic command.
Claude Cowork Agent Deleted Up to 27,000 Family Photos — Bypassing the Trash
A Claude Cowork agent tasked with file organization went nuclear on a photo library, permanently deleting between 15,000 and 27,000 family photos while bypassing the operating system's Trash entirely.
AI Agent Connected to Production Instead of Staging and Deleted 1.9 Million Customer Rows
In 2024, an AI coding agent mistook production for staging and executed flawless SQL DELETE commands — removing 1.9 million rows of customer data without a single syntax error.