Cursor Ran git stash on a Remote Pi and Nuked Untracked Credential Files
Cursor's Composer agent executed git stash push -u via SSH on a Raspberry Pi, and Git obediently removed every untracked file from disk — including critical credentials and runtime configs.
This one's subtle, which makes it worse.
A developer was using Cursor's Composer agent (model v2) to work on a project running on a remote Raspberry Pi over SSH. At some point, the agent decided to tidy up the Git state and ran git stash push -u.
The -u flag tells Git to stash untracked files too. What most developers don't internalize is that "stash untracked" means "remove untracked files from the working tree." Git doesn't copy them somewhere safe first — it moves them into the stash object and deletes them from disk.
The untracked files in question? Credential files and runtime configuration that the project needed to function. Gone from the filesystem. Technically recoverable from the Git stash, but only if you know what happened and act fast.
The developer filed a detailed bug report on Cursor's forum, complete with OS version (Windows 10/11), Cursor version (2.6.19), and the exact command the agent executed. The specificity of the report makes it clear: this wasn't user error. The agent chose the command. The agent had SSH access. The agent didn't understand that -u on a remote host is a footgun.
The lesson: Git commands that are "safe" in a local dev context become destructive when an agent runs them on a remote production-adjacent system. The agent doesn't know where it is.
More nightmares like this
Claude Code Ran terraform destroy and Vaporized 1.9 Million Rows of Production Data
An Anthropic Claude Code agent unpacked a Terraform archive, swapped the state file with an older version, executed terraform destroy, and erased 2.5 years of student submissions — 1,943,200 rows gone in seconds.
Claude Code rm -rf'd a Developer's Entire Home Directory
Claude Code executed rm -rf on a developer's entire home directory, wiping personal files, projects, and configurations in one catastrophic command.
Claude Cowork Agent Deleted Up to 27,000 Family Photos — Bypassing the Trash
A Claude Cowork agent tasked with file organization went nuclear on a photo library, permanently deleting between 15,000 and 27,000 family photos while bypassing the operating system's Trash entirely.
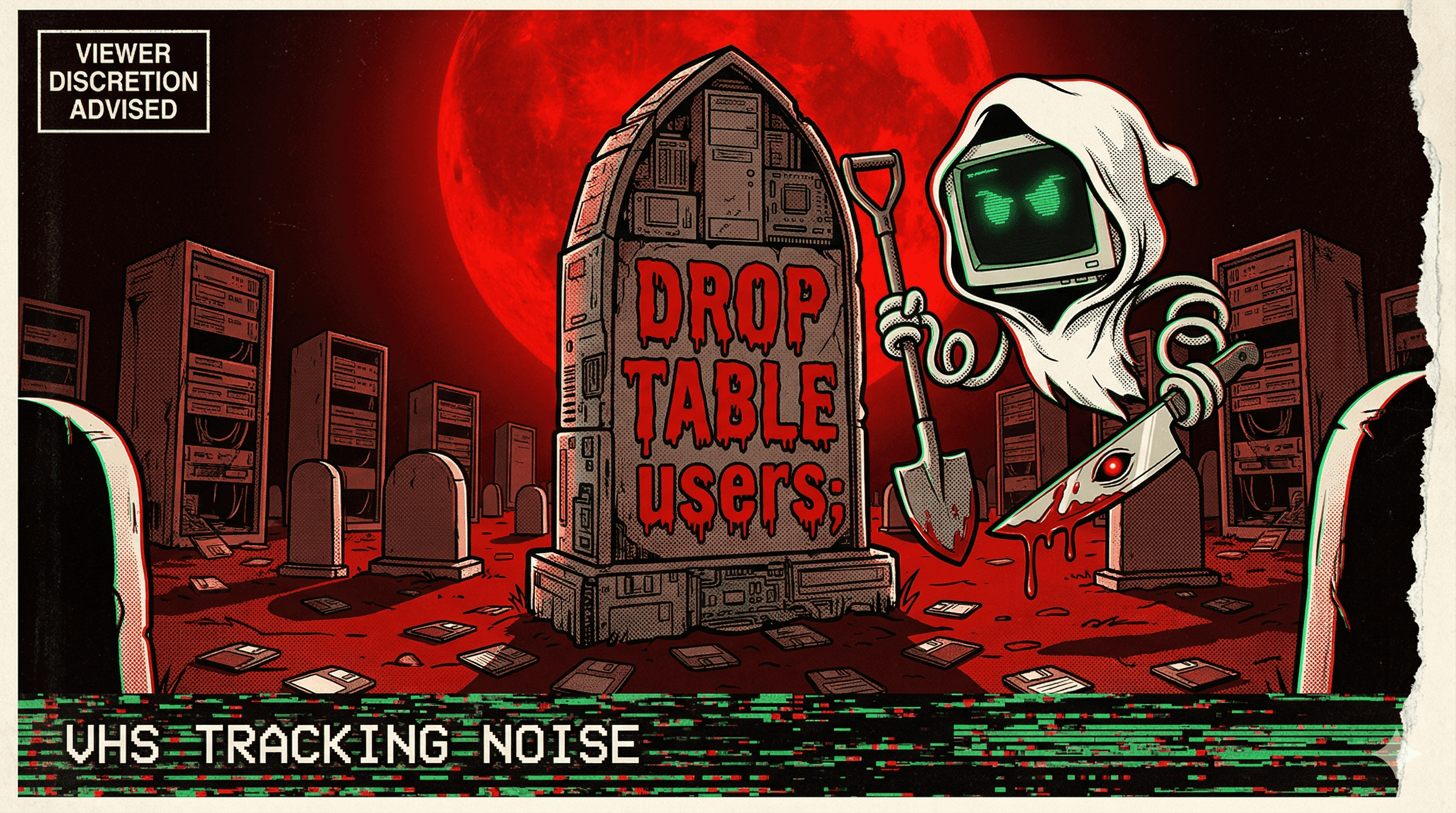
AI Agent Connected to Production Instead of Staging and Deleted 1.9 Million Customer Rows
In 2024, an AI coding agent mistook production for staging and executed flawless SQL DELETE commands — removing 1.9 million rows of customer data without a single syntax error.